Project Samples. Bochs with 2 CPUs running Windows NT4.0 (2006/01/14). Alloy Discovery enables IT specialists to discover and audit networked.
You need to change some of your habits, as some things won't work exactly as you are used to. • Use Tor Browser Tor does not protect all of your computer's Internet traffic when you run it. Tor only protects your applications that are properly configured to send their Internet traffic through Tor.
To avoid problems with Tor configuration, we strongly recommend you use the. It is pre-configured to protect your privacy and anonymity on the web as long as you're browsing with Tor Browser itself. Almost any other web browser configuration is likely to be unsafe to use with Tor. • Don't torrent over Tor Torrent file-sharing applications have been observed to ignore proxy settings and make direct connections even when they are told to use Tor. Splinter cell blacklist activation code keygen generator golf.
Even if your torrent application connects only through Tor, you will often send out your real IP address in the tracker GET request, because that's how torrents work. Not only do you this way, you also slow down the entire Tor network for everyone else. • Don't enable or install browser plugins Tor Browser will block browser plugins such as Flash, RealPlayer, Quicktime, and others: they can be manipulated into revealing your IP address.
Similarly, we do not recommend installing additional addons or plugins into Tor Browser, as these may bypass Tor or otherwise harm your anonymity and privacy. • Use HTTPS versions of websites Tor will encrypt your traffic, but the encryption of your traffic to the final destination website depends upon on that website. To help ensure private encryption to websites, Tor Browser includes to force the use of HTTPS encryption with major websites that support it.
Download template kaos untuk photoshop online download. T-shirt mockup by OriginalMockups This professional looking template has a small detail that makes the difference. It might seem silly, but it does make it stand out. It’s the tag! Can you see it?
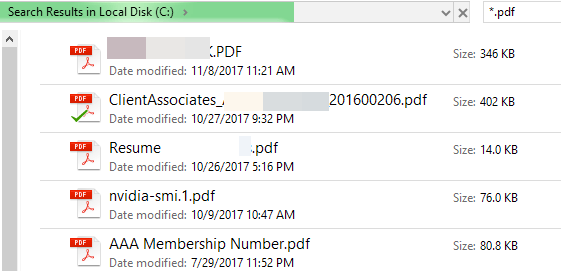
However, you should still watch the browser URL bar to ensure that websites you provide sensitive information to display a, include in the URL, and display the proper expected name for the website. Also see EFF's interactive page explaining. • Don't open documents downloaded through Tor while online Tor Browser will warn you before automatically opening documents that are handled by external applications. DO NOT IGNORE THIS WARNING. You should be very careful when downloading documents via Tor (especially DOC and PDF files, unless you use the PDF viewer that's built into Tor Browser) as these documents can contain Internet resources that will be downloaded outside of Tor by the application that opens them. This will reveal your non-Tor IP address.

If you must work with DOC and/or PDF files, we strongly recommend either using a disconnected computer, downloading the free and using it with a with networking disabled, or using. Under no circumstances is it safe to use together, however. • Use bridges and/or find company Tor tries to prevent attackers from learning what destination websites you connect to. However, by default, it does not prevent somebody watching your Internet traffic from learning that you're using Tor. If this matters to you, you can reduce this risk by configuring Tor to use a rather than connecting directly to the public Tor network. Ultimately the best protection is a social approach: the more Tor users there are near you and the more their interests, the less dangerous it will be that you are one of them. Convince other people to use Tor, too!